Researchers say Mythos sped Apple M5 Mac exploit development
Calif says Anthropic's Mythos Preview helped build a working exploit against Apple's M5 memory protections in five days, sharpening the Mac fleet security debate.

Security researchers at Calif say Anthropic’s Mythos Preview helped them build a working exploit against Apple’s M5-era Mac protections. The job took five days. The claim is drawing scrutiny to how quickly AI tools can compress offensive security work — and for organisations running Mac fleets, that matters.
Strip away the hyperventilating and the core question is simpler than it looks. Can newer safeguards be probed and tested much faster than defenders assume? Calif’s write-up suggests yes.
The firm says it produced the first public macOS kernel memory-corruption exploit on Apple M5 silicon, targeting macOS 26.4.1 (25E253). The defence it tested is Apple’s Memory Integrity Enforcement — MIE for short — a layer meant to make kernel memory attacks materially harder on newer Macs. That is not an Apple-enthusiast story. It sits squarely in enterprise security.
Apple spent about five years developing MIE, according to 9to5Mac’s account of the research. Calif said its engineers, working with Mythos Preview, delivered a working exploit in five days. Five years versus five days. Nobody is claiming that ratio proves Apple’s security model is collapsing. But it does suggest AI can help offensive teams move from theory to proof-of-concept at a pace that rewrites patching and hardening assumptions.
Apple was alerted before the report went public. A spokesperson told MacRumors the company treats vulnerability reports seriously and that security is its top priority. That is what Apple always says. The sharper takeaway for IT teams is operational: if AI-assisted researchers can pressure-test new mitigations this quickly, Mac fleet risk turns on patch speed and endpoint visibility more than on any single hardware defence.
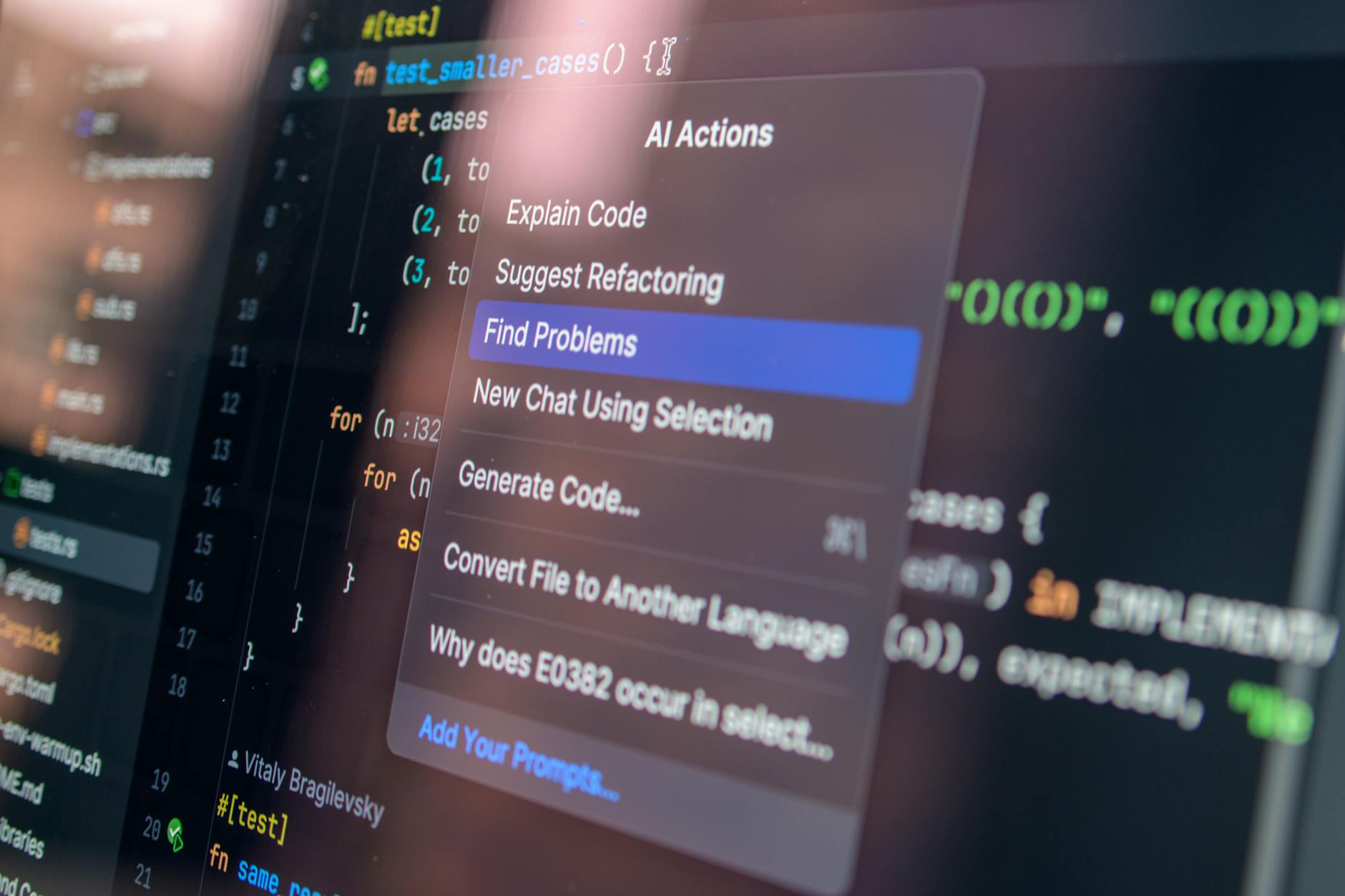
One thing the episode does not show. Mythos did not independently compromise Apple systems, and M5-based Macs are not suddenly easy targets. Calif described a human-led workflow. The AI model accelerated parts of it — iteration, code refinement, attack-path exploration. For defenders that distinction matters. The threat is not one reported exploit. It is the gap. Capable teams using models from vendors like Anthropic can now close the distance between a new defensive control shipping and public offensive work catching up faster than many assumed possible.
Calif’s report comes from a lab, but defenders read lab proofs-of-concept as early signals. That is especially true for businesses that run Macs for executives, developers or creative teams. A kernel-level weakness carries outsized consequences even without evidence of broad exploitation.
For security leaders managing large Mac estates the practical lesson is not complicated. Hardware-backed mitigations still count, but they do not replace fast patch validation, close endpoint monitoring and clear-eyed assumptions about what AI-assisted researchers can do against high-value platforms. Calif’s claim will need weighing against Apple’s own response. Even now, it is a reminder that the speed of offensive research has changed.
Reza Khalil
Cybersecurity reporter covering breaches, threat intel, and the ACSC beat. Former incident responder. Reports from Canberra.